Resources and Best Practices to
Help Secure Your Remote Workforce
Overnight, your workforce moved from your offices to their homes, creating a myriad of security challenges. What are the impacts?
Your employees are using managed and unmanaged devices to access the data and cloud applications they need to do their jobs. Symantec can help your organization protect every authorized user and every device, ensuring safe access to email, web and cloud while protecting vital corporate data and identities.
Need Help Managing your Remote Workforce?

BLOGS
Stay up-to-date with the latest blogs from our security engineers and threat analysts, who are closely tracking new attacks attempting to leverage public fears about COVID-19.
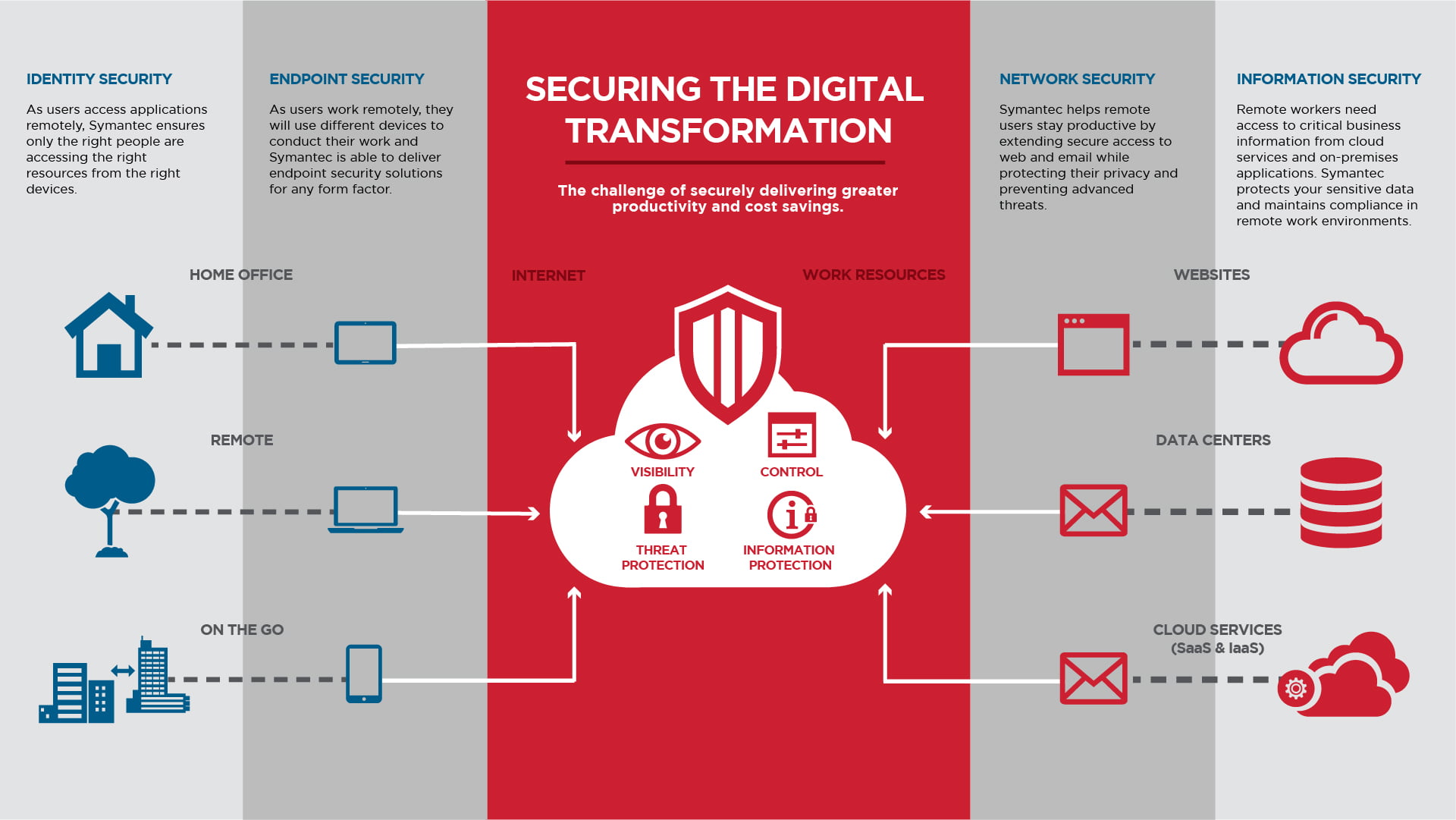
Explore Our Solutions for Securing Your Remote Workforce

IDENTITY SECURITY
As employees access applications, Symantec ensures only the right people are accessing the right resources from the right devices.

ENDPOINT SECURITY
As employees work remotely, they will use different devices to conduct their work and Symantec delivers endpoint security solutions for any form factor.

NETWORK SECURITY
Symantec helps remote workers stay productive by extending secure access to web and email while protecting their privacy and preventing advanced threats.

INFORMATION SECURITY
Remote workers need access to critical business information from cloud services and on-premise applications. Symantec protects your sensitive data and maintains compliance in remote work environments.
Protect Remote Workers from Risk
Check out the infographic to see how Symantec reduces risk for remote workers, empowering them to be more efficient and productive.